
Barracuda PhishLine
Fight phishing with continuous simulation and training
*Price per User.
Our Price: Request a Quote
*Price per User. Quantity must be 250 or greater.
Our Price: Request a Quote
More pricing below, click here
Please Note: All Prices are Inclusive of GST
Overview:
Barracuda’s Security Awareness Training platform enables users to understand and respond correctly to the latest phishing techniques, recognize subtle phishing clues, and prevent email fraud, data loss, and brand damage. It transforms employees into a powerful line of defense against damaging phishing attacks.
This versatile, cloud-hosted solution includes hundreds of customizable email and landing page templates, frequently updated based on the latest threat trends. A large library of micro-learning videos and training content keeps users engaged.
Simulate threats
Hundreds of real-world threat templates, expose your users to the latest threat types. Simulations are not limited to email but also include SMS, voice and portable media (USB drive) attacks.
Analyze behavior
Advanced analytics and reporting tools identify how users respond to threat simulations and help implement an effective training program.
Educate users
A large content library of engaging training videos, games and other material, equips you to meet your unique awareness initiatives.
Simplify security awareness.
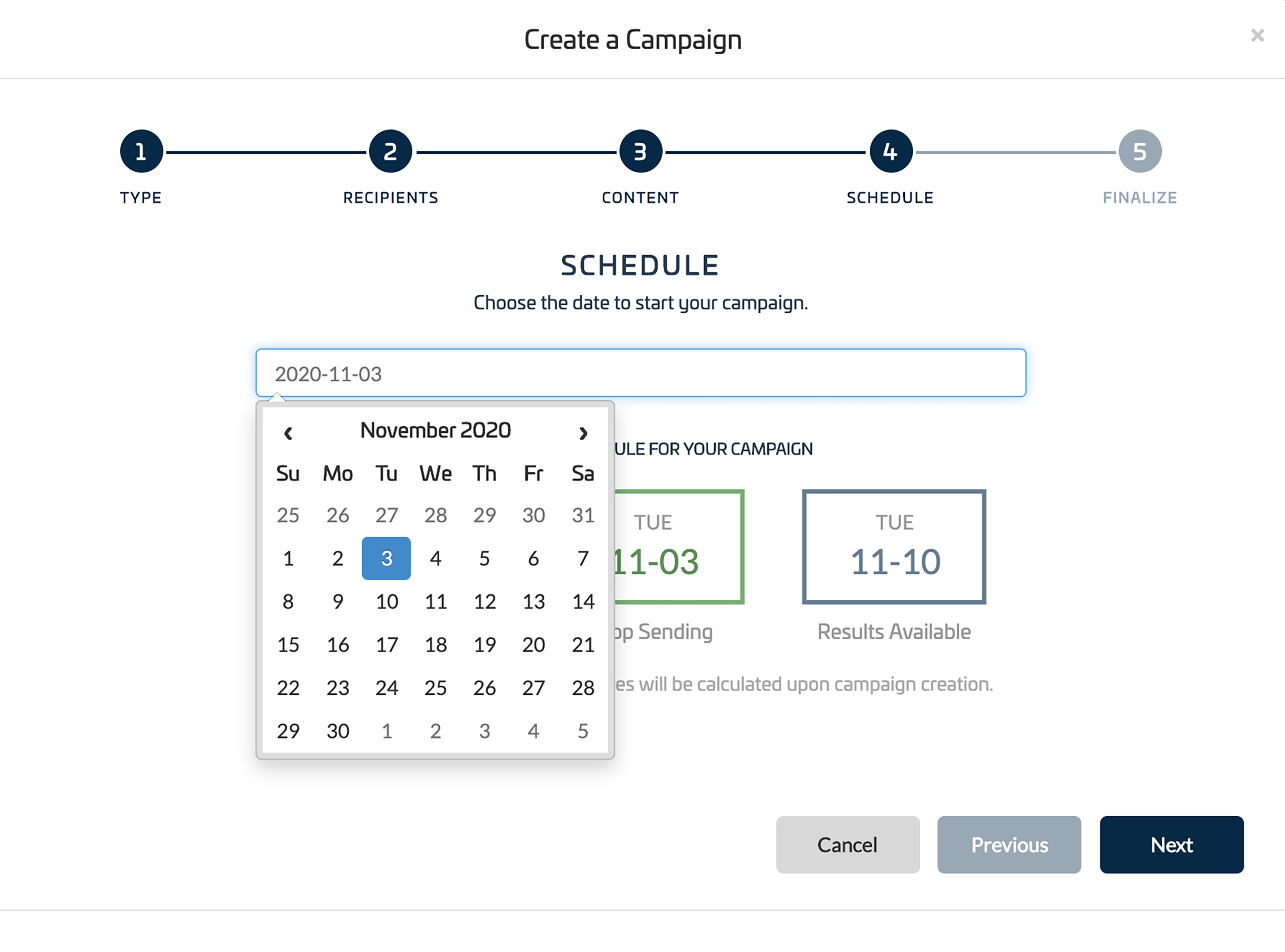
Security Awareness Training gives you the option to create a completely customized program or opt for the Quick Launch process to get an awareness campaign up and running in under a minute. Quick Launch simplifies security awareness with an easy 5-step setup, proven curated testing and training content, and efficient, automated reports.

Empower users to defeat the 13 email threat types.
Barracuda Email Protection stops over 20,000 spear phishing attacks every day. Security Awareness Training leverages that extensive threat intelligence to create real-world simulation and training content aligned with all identified 13 email threat types. Users will learn to spot business email compromise, impersonation attacks and other top email threats.
Gain real insights into your biggest vulnerabilities.
Security Awareness Training captures thousands of data points to give you deeper and more useful insights into exactly where your risks exist so you can precisely target your awareness programs.
- User-behavior metrics
- Detailed trend analytics
- Benchmarking statistics
- Customizable reports and dashboards
Meet compliance with specially-designed training.
When security awareness training requirements are mandatory, it’s not always clear where to begin. Security Awareness Training includes ready-to-launch training designed by our experts to meet compliance requirements, making it easy for your organization to meet regulations, fight security risks, and stay secure.

Keep security top-of-mind with engaging awareness material.
Continuous training is most effective at influencing user behavioral change. Leverage the monthly ClickThinking™ content bundles of infographics, posters, and additional videos to supplement training campaigns and cultivate your security culture.
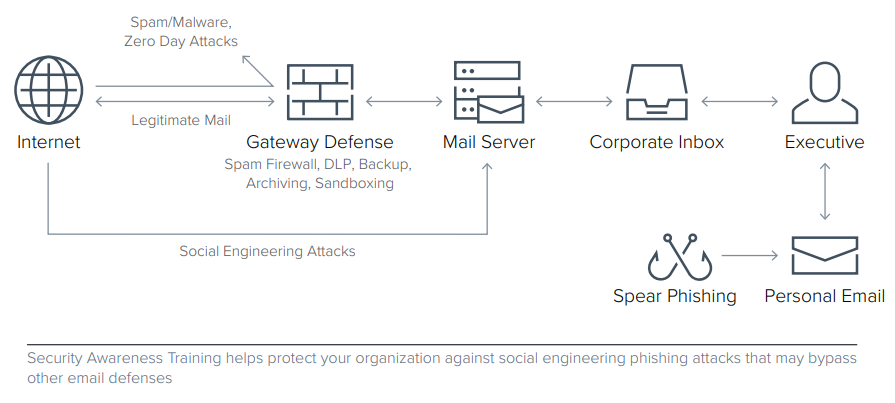
Make training part of a comprehensive security strategy.
Barracuda offers a complete solution that delivers security awareness training, gateway defense, API-based inbox defense, incident response, data protection, and compliance capabilities. Barracuda Email Protection eliminates the integration and support headaches that typically come along with piecemeal, multi-vendor solutions.
Features:
Content
- Hundreds of email lure templates, landing pages, and domains
New content is added, every day creating endless combinations of email templates, landing pages, email account senders, and web server domains. As the threat landscape changes so will our tests, giving you access to the most up-to-date content. - Content Center Marketplace
All content can be found in the Content Center Marketplace, a one-stop shop for browsing, selecting, and importing the perfect content to craft your continually evolving campaigns. - Customized templates
Add that special touch by customizing any of the templates, so your simulated attacks come from people in positions of trust, effectively testing your workforce and teaching them to be wary of threats that only your organization may have seen.
Testing
- Patented multi-variable attack simulations
In today's threat landscape, you can be phished from more than just email. Train your team on every facet of threat with Barracuda's multi-variable campaigns that include Smishing (SMS/Text), Vishing (Voicemail) and Found Physical Media. This unique capability will help prevent users from receiving the same mock phishing template in a campaign and can allow for hypothesis-based testing (A/B tests). - Smishing (SMS/text)
Protect your user base by training them to recognize unfamiliar outgoing texts with our industry-leading smishing simulation. The innovative incoming mode allows you to email requests to text custom phone numbers as the call-to-action for otherwise innocuous emails, catching what would be a normally unknown vector before it can be used against your workforce. - Vishing (voicemail)
Employees get many phone calls each day. Which one of those will cost the company? With Barracuda's anti-voicemail phishing, or 'vishing,' we provide fully customizable simulated threats that will complement any security awareness campaign. - Found physical media (USB/SD Card)
Using the same Smart Attachment technology found in our email campaigns, you can distribute files on portable drives and cards with watermarks in a variety of file formats to track who is willing to plug it into your network. The files won't cause security problems even if non-employees find them as the content redirects users to landing pages designed to educate on the perils found in anonymous portable media. - Advanced threat simulation features
Crafting effective scenarios is paramount when developing an effective anti-spear-phishing campaign, especially in long-term approaches where users would start seeing repetitive emails. Prevent that by using Barracuda's advanced threat simulation features, including time stamping to create a sense of urgency, prompting users to respond before they can think it through, phone home macros, DLP tagging, geolocation, and more. Our patented system allows for multiple combinations of email templates, landing pages, email account senders, and web server domains in a single campaign.
Reporting
- Phish Reporting Button
Enable easy tracking of user phishing attempts with the Phish Reporting Button, simplifying the task of reporting possible threats while tying in user reporting to your training regimen. - Robust user attributes
Why stop at username and email address, when you can test based on location, job function, tenure, privileged credentials, and access to sensitive networks and applications? Barracuda gives you granular control of your reports, such as that your mid-level marketing managers in Kansas are more likely to click a link in an email on Tuesday, as well as testing and education, so your workforce isn't inundated with emails they shouldn't get. - Extensive reporting and metrics
More than 16,000 data points are at your disposal with Barracuda's advanced metrics and reporting. Identify levels of risk at macro and micro levels in your organization, to help expedite remediation while keeping your workforce at maximum efficiency by targeting training to only those who need testing at that moment. - Data loss prevention (DLP)
Worried about data leaking from your organization? With Barracuda's built-in Data Loss Prevention Activator, you can track where those campaign emails and portable media drops go and who accesses it, to know who might leak your company data as well. - HTTP/SSL
Is your workforce leaning hard on whether there's an encryption symbol next to the URL when they click links in their emails? With HTTPS and SSL landing pages you can collect information from your users without the possibility of people snooping that information and using it against you, while convincing your users that they are safe.
Education
- Program gamification
Engage your users and make the cat-and-mouse aspect of security awareness fun by turning the workflow into a game with leaderboards and user-leveling systems. This will help train users to spot and report threats while keeping the idea of spear phishing at the forefront of their mind. - Risk-based surveys
Should a CEO or accounts payable team get the same test as your engineer, nurse, or teacher? With Barracuda, you can issue risk-based surveys that provide unique insights into your user-level security posture. By being better informed about your user-level risk and validating it throughout the year, you will maintain a security plan that mirrors your organizational objectives. - Bonus security awareness training materials
To support your computer-based training initiatives, Barracuda provides supplementary materials, such as two-minute best practice videos covering topics like malware awareness and password security. In addition, there is an array of bonus training materials, including posters, newsletters, infographics, and tip sheets. Barracuda has partnered with several reputable content vendors to augment our built-in content.
Plans:
Security Awareness Training is included as part of Barracuda Email Protection Premium Plus. Find the plan that’s right for you.

- Combine email gateway and artificial intelligence to block threats.
- Ensure protection against all 13 email threat types.
- Automatically remediate post-delivery email threats.

- Includes everything from Advanced.
- Protect your brand from domain fraud.
- Make web browsing safe for your users.
- Automate post-delivery threat hunting and response.

- Includes everything from Premium.
- Improve user security awareness.
- Protect and restore your Office 365 data.
- Discover sensitive data and undetected stored malware.
- Demonstrate compliance with regulatory requirements.
| Capabilities | Advanced | Premium | Premium Plus |
|---|---|---|---|
| Spam and Malware Protection Identify and block spam, viruses, and malware delivered via email messages. Using virus scanning, spam scoring, real-time intent analysis, URL link protection, reputation checks, and other techniques, Barracuda scans email messages and files. |
|||
| Attachment Protection Barracuda combines behavioral, heuristic, and sandboxing technologies to protect against zero-hour and targeted attacks. A sandbox environment is used to detonate and observe behavior of suspicious attachments. |
|||
| Link Protection Link Protection automatically rewrites URLs so that Barracuda can sandbox the request at click time to block malicious links. |
|||
| Email Continuity In the event of a mail server outage or loss of connectivity, an emergency mailbox lets users continue to send and receive emails, staying productive until your primary servers are back online. |
|||
| Email Encryption Secures your mail by encrypting it during transport to the Barracuda Message Center, encrypting it at rest for storage in the cloud, and providing secure retrieval by your recipients through HTTPS web access. Create a policy to automatically encrypt emails based on their sender, content, and other criteria. |
|||
| Data Loss Prevention Create and enforce content policies to prevent sensitive data, including credit card numbers, Social Security numbers, HIPAA data, customer lists, and other private information, from being sent by email. Policies can automatically encrypt, quarantine, or block certain outbound emails based on their content, sender, or recipient. |
|||
| Phishing and Impersonation Protection Automatically detect and prevent impersonation, business email compromise, and other targeted attacks. Barracuda's AI engine learns each organization's unique communication patterns and leverages these patterns to identify anomalies and prevent socially engineered attacks in real time. |
|||
| Account Takeover Protection Stop phishing attacks used to harvest credentials for account takeover. AI detects anomalous email behavior and alerts IT, then finds and removes all fraud emails sent from compromised accounts. |
|||
| Automatic Remediation All user-reported messages are automatically scanned for malicious URLs or attachments. When a threat is detected, all matching emails are automatically moved from users' mailboxes into their junk folders. |
Threat Hunting and Response Quickly identify and efficiently remediate post-delivery threats by automating investigative workflows and enabling direct removal of malicious emails. |
||
| Automated Workflows Build custom playbooks to completely automate your incident response process. Admins at any technical level can create a workflow by defining a trigger, determining conditions, and assigning the desired actions through a simple user interface. |
|||
| SIEM/SOAR/XDR Integration Orchestrate incident response cross-product with RESTful API (beta) and syslog integrations. Remotely administer and configure incident response capabilities and store your event data for tracking, analysis, and troubleshooting. |
|||
| Domain Fraud Protection Prevent email domain fraud with DMARC reporting and analysis. Barracuda provides granular visibility and analysis of DMARC reports and helps you minimize false positives, protect legitimate email, and prevent spoofing. |
|||
| DNS Filtering Protect users from accessing malicious web content with advanced DNS and URL filtering. |
|||
| Cloud Archiving A cloud-based, indexed archive allows for granular retention policies, extensive search, role-based auditing/permissions, legal hold, and export. Easily comply with e-discovery requests and regulatory or policy-retention requirements. |
|||
| Cloud-to-Cloud Backup Get data protection and cloud backup for Office 365 data, including Exchange Online mailboxes, SharePoint Online, OneDrive for Business, and Teams. Fast point-in-time recovery in the event of accidental or malicious deletion. |
|||
| Data Inspector Automatically scan your OneDrive for Business and SharePoint data for sensitive information and malicious files containing malware. Use it to develop policies that comply with GDPR, CCPA, and other data privacy regulations. |
|||
| Attack Simulation Simulated phishing attacks are constantly updated to reflect the most recent and most common threats. Simulations are not limited to email, but also include voice, SMS, and portable-media (USB stick) attacks. |
|||
| Security Awareness Training Get access to advanced, automated education technology that includes simulation-based training, continuous testing, powerful reporting for administrators, and active incident-response awareness. |
Documentation:
Download the Barracuda Security Awareness Training Datasheet (PDF).
Pricing Notes:
- All Prices are Inclusive of GST
- Pricing and product availability subject to change without notice.
*Price per User.
Our Price: Request a Quote
*Price per User. Quantity must be 250 or greater.
Our Price: Request a Quote
*Price per User. Quantity must be 1,000 or greater.
Our Price: Request a Quote
*Price per User. Quantity must be 2,500 or greater.
Our Price: Request a Quote
*Price per User. Quantity must be 10,000 or greater.
Our Price: Request a Quote
*Price per User. Quantity must be 100 or greater.
Our Price: Request a Quote
*Price per User. Quantity must be 2,000 or greater.
Our Price: Request a Quote
*Price per User. Quantity must be 10,000 or greater.
Our Price: Request a Quote
*Price per User. Quantity must be 25,000 or greater.
Our Price: Request a Quote
Our Price: Request a Quote


